In a distributed environment like ENACT, applications do not only need computing resources but they also need a reliable way to store, discover, share, and retrieve data and digital objects across the continuum. This is the role of the ENACT Data Space, one of the core building blocks of the project’s Data Layer. Rather than acting as a conventional storage backend, it is designed as a secure, sovereign, and interoperable environment in which different ENACT components and participants can exchange assets while preserving control over who can access them and under what conditions.
This point is important because ENACT is not based on a centralized platform logic. Its architecture spans different layers, nodes, and stakeholders. The Data Layer has been designed to support the storage of historical telemetry data, AI training datasets, and code objects, while also handling authentication, authorization, metadata management, and distributed storage. In architectural terms, the Data Layer includes three main elements: the Data Access and Sharing Interfaces, the Data Manager, and the Data Stores. Together, these components provide the practical implementation of the ENACT Data and Object Space.
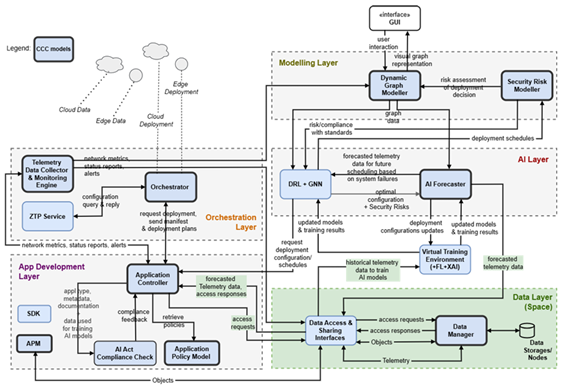
Figure 1: Data Layer position in ENACT Architecture
What makes the ENACT Data Space especially relevant is the concept on which it is built. The project frames it around the idea of Data Spaces, understood as federated infrastructures for sovereign data sharing based on common rules, policies, and standards. In contrast to traditional centralized platforms, a Data Space allows data providers to remain in control of their assets while still participating in a shared ecosystem. This means that ENACT is not just creating a storage repository, it is creating a governed environment for trusted exchange.
At the technical level, the Data Space relies heavily on Data Space Connectors, which act as the gateways through which participants publish, discover, negotiate, and transfer assets. ENACT selected the sovity connector, built on top of the Eclipse Data Connector and aligned with IDS and Gaia-X specifications. This is a strong design choice because it anchors the ENACT solution in existing European data-sharing standards rather than inventing a closed, project-specific mechanism. The connector layer supports the creation of policies, contract negotiation, controlled transfers, and the enforcement of usage conditions.
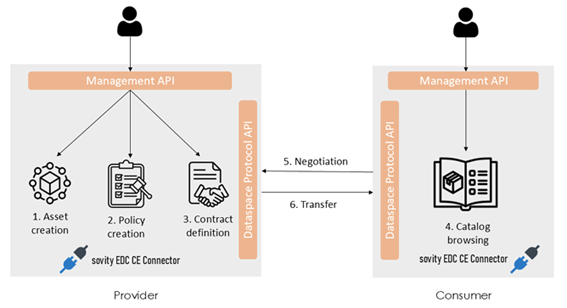
Asset sharing workflow through sovity connectors
One particularly interesting aspect of ENACT’s approach is that the Data Space supports not only data sharing, but also object sharing. ENACT extends the Data Space concept so that code objects, such as executable scripts or reusable artefacts, can also be exchanged. These objects can later be retrieved by the SDK during application development. This gives the Data Space a much more strategic role inside the project. It is not only a place for storing monitoring outputs or AI-related data; it is also a mechanism for developer collaboration, reusability, and faster application development.
Security and trust are another major pillar of the ENACT Data Space. The Data Manager includes a Security and Access Control Manager based on Keycloak, integrated with a DAPS-oriented identity model to support authenticated connector-to-connector communication. This enables participants to exchange assets through controlled authentication and authorization flows, while also supporting role-based access and secure credential handling. On top of that, the Data Manager includes a Metadata Manager, which enriches stored assets with searchable metadata and supports indexing, filtering, and retrieval. This is essential because in a distributed environment, storing assets is not enough; they also need to remain discoverable and manageable across nodes.
Ultimately, the ENACT Data Space is much more than a technical repository. It is a governed exchange environment that connects telemetry, AI workflows, application development, and pilot operations. By combining sovereign sharing, metadata-rich storage, distributed nodes, policy enforcement, and support for reusable code objects, it helps turn the ENACT continuum into a platform where data and digital assets can move securely, meaningfully, and productively across layers and participants.